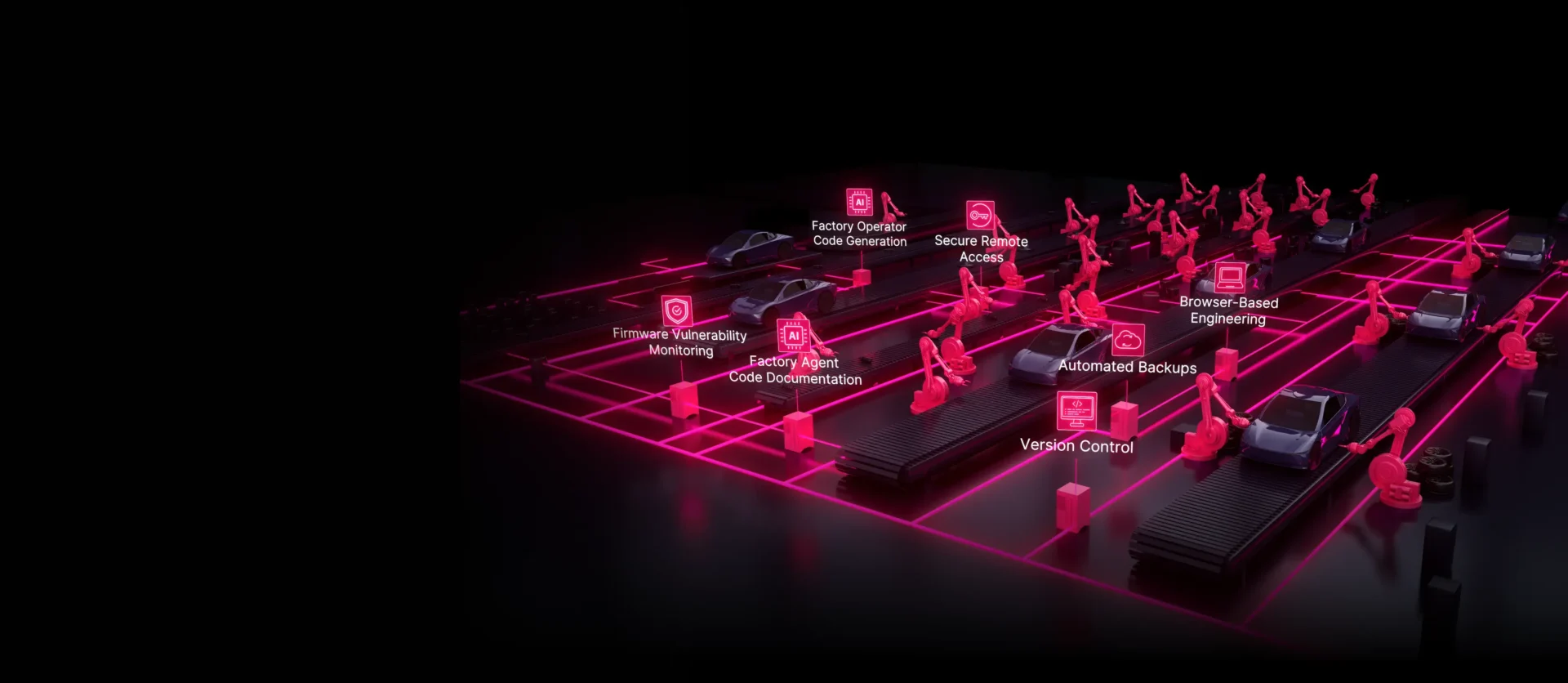
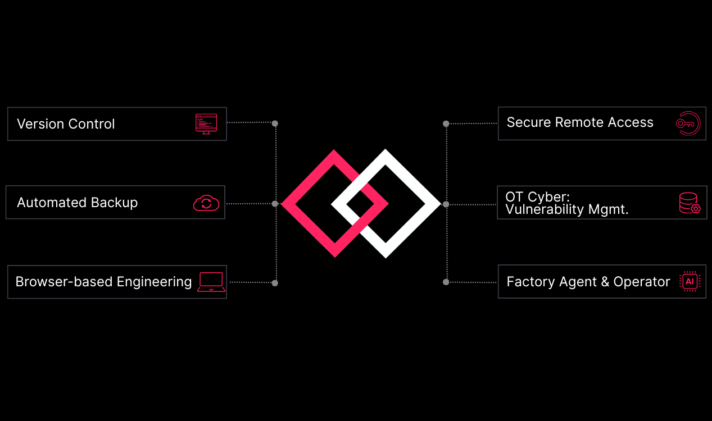
Software Defined Automation reimagines industrial operations by turning factories into dynamic, intelligent, and secure digital ecosystems. Our vision is a world where automation systems adapt as swiftly as software—empowered by AI insights, protected by built‑in OT security, and managed seamlessly across the globe.
By unifying control, intelligence, and security, we enable enterprises to continuously optimize performance, prevent downtime before it occurs, and innovate without constraints. In this future, every machine learns, every process self‑optimizes, and every operation is both resilient and transparent—driving a new era of industrial autonomy and trust.